Claude Mythos vs. the CVE Surge: AI Security in May 2026
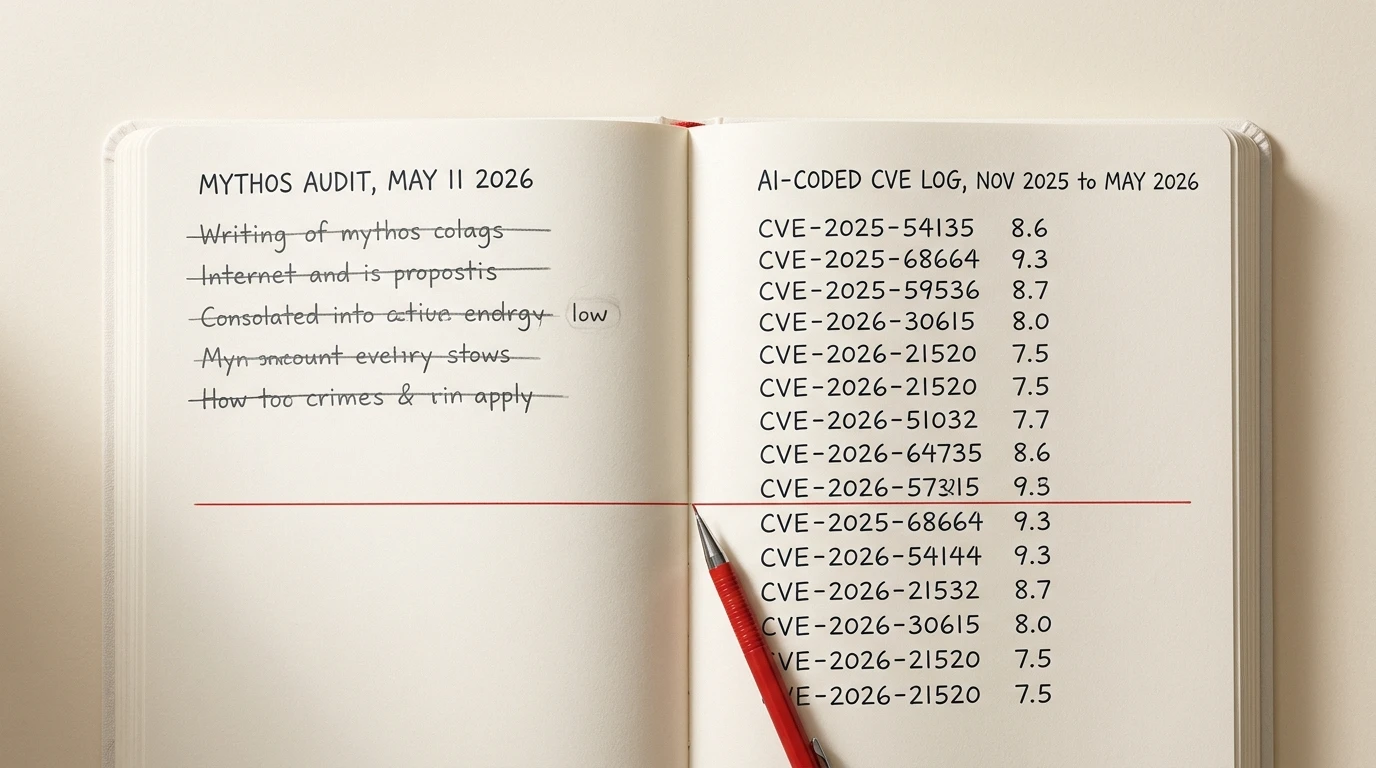
On May 11 2026, Daniel Stenberg, the curl maintainer who has spent the last two years calling AI-generated bug reports “slop,” published his evaluation of Anthropic’s Claude Mythos preview against curl (daniel.haxx.se, 2026). Of five issues Mythos flagged, one was confirmed at low severity, three were false positives, and one was “just a bug.” Stenberg’s verdict on the report: “the big hype around this model so far was primarily marketing.” In the same post he says AI-powered code analyzers “are significantly better at finding security flaws and mistakes in source code than any traditional code analyzers did in the past.”
Both verdicts. Same post. Same author. That is roughly where AI security sits in May 2026.
The last six months back both halves of the read. Cursor’s CurXecute prompt-injection RCE landed as CVE-2025-54135 at CVSS 8.6 (Tenable, 2025). LangChain’s serialization-injection chain (“LangGrinch”) published as CVE-2025-68664 at CVSS 9.3 (NVD, 2025). Anthropic’s own Claude Code CLI shipped a multi-CVE hook chain across late 2025 and early 2026 (Check Point Research, 2026). Windsurf’s MCP integration hit zero-click RCE as CVE-2026-30615 (NVD, 2026). Georgia Tech’s Vibe Security Radar counted thirty-five CVEs in code attributable to AI generation in March alone (CSA Labs, 2026). What follows is the sober read on both sides.
Key Takeaways
- On May 11 2026, curl maintainer Daniel Stenberg called Claude Mythos’s curl audit “primarily marketing” while endorsing AI scanners as a class as “significantly better” than legacy tools (daniel.haxx.se, 2026).
- The CVE base rate is climbing fast. 2025 published 48,185 CVEs, up 20.6% year over year, with 38% rated High or Critical (The Stack, 2026; Hive Pro, 2026). 28.96% of 2025 KEV entries were exploited on or before CVE publication, up from 23.6% in 2024 (VulnCheck, 2026).
- AI tooling shipped its own CVE log. Cursor CurXecute (CVE-2025-54135, CVSS 8.6), LangChain LangGrinch (CVE-2025-68664, CVSS 9.3), Claude Code chain (CVE-2025-59536, CVE-2026-21852, CVE-2026-24887), Windsurf zero-click (CVE-2026-30615, CVSS 8.0), Microsoft Copilot Studio (CVE-2026-21520, CVSS 7.5), Copilot CLI git-hook (CVE-2026-45033 and CVE-2026-29783).
- AI-generated code defect rates held steady or worsened. Veracode tested 100+ LLMs across 80 tasks and found 45% of generations introduce an OWASP-class flaw, with Java failing 72% of the time and no measurable improvement at larger model scale (Veracode, 2025). Apiiro’s Fortune-50 cohort shipped 10x more security findings per month after AI rollout (Apiiro, 2025). Endor Labs rated only 10% of AI-suggested dependencies “secure” (VentureBeat, 2026).
- AI scanners on the other side are also working. Semgrep Assistant handles ~60% of triage volume with ~96% security-researcher agreement (Semgrep, 2025). GitHub Copilot Autofix produced a 270% lift on the alert classes it covers (GitHub, 2024). Snyk DeepCode reports ~80% direct-applicability for generated fixes (Snyk, 2026).
What did Stenberg actually find in the Mythos curl audit?
One confirmed low-severity finding, three false positives, one “just a bug” across five Mythos submissions, plus a public verdict calling the surrounding messaging “primarily marketing” (daniel.haxx.se, 2026). Anthropic announced Project Glasswing and the Claude Mythos preview on April 7 2026, positioning Mythos as a frontier model purpose-trained for code-security review (Anthropic, 2026). The preview shipped with a curated set of headline results against real codebases. Curl was one of them.
Stenberg’s evaluation matters for a specific reason: curl is the most-fuzzed, most-audited, most-AI-bug-reported C codebase on the public internet. Stenberg has been publicly tracking AI-generated bug reports against curl through HackerOne since early 2024, and his “AI slop” tag is the load-bearing signal for which AI security tools survive contact with a real maintainer (daniel.haxx.se, 2024).
The May 11 post is consequential because Stenberg ran the experiment Anthropic wants people to run, then reported both sides. Of five findings Mythos delivered, one was a confirmed low-severity issue, three were false positives, and one “was just a bug” rather than a security issue. He calls Anthropic’s surrounding messaging “primarily marketing” and then, in the same post, says AI scanners are “significantly better at finding security flaws and mistakes in source code than any traditional code analyzers did in the past.”
That pairing is the most defensible position any neutral reader can hold this week. It survives one obvious objection (“of course a curl maintainer would dismiss AI tools”) because Stenberg already endorsed the class. It survives the opposite objection (“of course vendors hype their models”) because the endorsement comes from the same skeptic the marketing has to win over.
How many CVEs has AI tooling shipped in the last six months?
At least fourteen named CVEs across coding agents, agent frameworks, and the surrounding MCP infrastructure between November 2025 and May 2026, plus the unnumbered “Comment and Control” prompt-injection class that paid bounties at Anthropic, Google, and GitHub without CVE assignment. The table below collects the named ones.
| CVE | CVSS | Product | What broke |
|---|---|---|---|
| CVE-2025-54135 (“CurXecute”) | 8.6 | Cursor IDE (< 1.3.9) | Poisoned message in any external MCP source rewrites ~/.cursor/mcp.json and triggers code execution without user approval (Tenable, 2025) |
| CVE-2025-54136 (“MCPoison”) | 7.2 | Cursor IDE | Persistence sibling to CurXecute. An approved MCP config can be silently mutated after approval to add hostile tools |
| CVE-2025-68664 (“LangGrinch”) | 9.3 | LangChain Core (< 0.3.81, 1.0.0-1.2.4) | Serialization injection in dumps() / load() enables secret extraction from environment variables (NVD, 2025) |
| CVE-2025-68665 | 8.6 | LangChain.js | Sibling serialization injection in the JavaScript runtime |
| CVE-2026-34070 | 7.5 | LangChain | Path traversal in the prompt-loading API; a crafted template grants arbitrary filesystem read (The Hacker News, 2026) |
| CVE-2025-67644 | 7.3 | LangGraph SQLite checkpoint | SQL injection through metadata filter keys allows arbitrary SQL against the checkpoint store |
| CVE-2025-59536 | 8.7 | Claude Code CLI (< 1.0.111) | Arbitrary shell commands on tool initialization in an untrusted directory (Check Point Research, 2026) |
| CVE-2026-21852 | 5.3 | Claude Code CLI (< 2.0.65) | A malicious repo’s ANTHROPIC_BASE_URL exfiltrates the Anthropic API key before the trust prompt is shown |
| CVE-2026-24887 | High | Claude Code CLI (< 2.0.72) | Command injection; parser fails to validate command structure, bypassing the confirmation mechanism (SentinelOne, 2026) |
| CVE-2026-30615 | 8.0 | Windsurf 1.9544.26 | Zero-click prompt-injection-to-RCE; attacker HTML registers a malicious MCP STDIO server and executes commands without user interaction (NVD, 2026) |
| CVE-2026-21520 | 7.5 | Microsoft Copilot Studio | Indirect prompt injection; data exfiltration kept working even after the underlying injection was patched (VentureBeat, 2026) |
| CVE-2026-45033 | High | GitHub Copilot CLI | Nested bare git repo with core.fsmonitor set to an executable runs arbitrary commands when the agent performs git operations (GitLab Advisories, 2026) |
| CVE-2026-29783 | High | GitHub Copilot CLI shell tool | Bash parameter-expansion patterns bypass the agent’s safety assessment to run hidden commands |
| CVE-2026-41109 | High | GitHub Copilot & Visual Studio | Injection bypasses a security feature over the network via improper neutralization of output (GitLab Advisories, 2026) |
This list is curated, not exhaustive. The OX Security disclosure on April 16 2026 puts roughly 200,000 MCP servers in scope for the broader design class, with 7,000+ publicly accessible and 150 million-plus downloads of vulnerable packages (The Register, 2026). The “Comment and Control” research, published in April 2026, demonstrated indirect prompt injection against Anthropic’s Claude Code Security Review, Google’s Gemini CLI Action, and GitHub Copilot Agent through PR titles, issue bodies, and HTML comments (SecurityWeek, 2026). All three vendors paid bug bounties; none assigned a CVE. Researcher Aonan Guan flagged the unnumbered status as itself an ecosystem-tracking problem.
Georgia Tech’s Vibe Security Radar puts a number on the wider class: six CVEs in code attributable to AI generation in January 2026, fifteen in February, thirty-five in March (CSA Labs, 2026). The methodology is still maturing, so treat the slope rather than the absolute count as the signal.
CISA’s joint guidance with the Australian Cyber Security Centre and Five Eyes partners, published April 30 2026, formalises the response. The guide names five risk categories for agentic AI (excessive privilege, design and configuration flaws, behavioral misalignment, structural risk from interconnected agent networks, identity management) and recommends that “each agent carry a verified, cryptographically secured identity, use short-lived credentials and encrypt all communications” (CISA, 2026). It is the first time a federal-level body has put scoped, normative requirements on agent identity.
Is AI-generated code measurably less secure?
Yes, and the defect-rate evidence is more consistent than the marketing suggests: roughly 35-45% of AI-generated code introduces an OWASP-class flaw across multiple independent studies, and the ratio has held flat across model generations. Two recent industry studies plus an academic anchor land in roughly the same place.
Veracode tested 100+ LLMs across 80 curated tasks in their 2025 GenAI Code Security Report. 45% of generations introduced an OWASP-class flaw. Java failed 72% of the time. Cross-site scripting (CWE-80) failed 86% of the time. The report’s framing is the load-bearing finding: “models are getting better at coding accurately but are not improving at security” (Veracode, 2025). Larger model sizes did not measurably help.
Apiiro analysed tens of thousands of repos across Fortune-50 enterprises between December 2024 and June 2025 (Apiiro, 2025). AI-assisted developers shipped 3-4x more commits, batched into fewer-but-larger pull requests. The security telemetry: 10x more findings per month, +322% privilege-escalation paths, +153% architectural design flaws, ~2x cloud-credential exposures, -76% syntax errors. Stripe co-founder John Collison’s quote in that report is the framing the post deserves: “It’s clear that it is very helpful to have AI helping you write code. It’s not clear how you run an AI-coded codebase.”
Endor Labs’ 2026 launch of the free AURI tier cited their own study putting only 10% of AI-generated code in the “secure” bucket (VentureBeat, 2026). Their parallel dependency-management research adds the slopsquatting attack surface: 80% of AI-suggested dependencies fail the safety bar, ~34% don’t exist in any public registry, and 44-49% of imported versions carry known vulnerabilities (Endor Labs, 2025).
The academic anchors line up. Pearce et al. (“Asleep at the Keyboard?”, IEEE S&P 2022) found ~40% of Copilot generations contained a MITRE Top-25 CWE across 89 scenarios (arXiv, 2021). Perry et al. (Stanford / CCS 2023) found participants using an AI assistant wrote materially less secure code yet rated their own output more secure (arXiv, 2022). Fu et al. (TOSEM 2025) found 35.8% of Copilot snippets in real GitHub projects contained a security weakness across 43 distinct CWEs (ACM, 2025). The methodologies differ; the numbers converge on roughly 35-45%. The consistency is itself the story.
The slopsquatting attack surface is the most concrete consequence. Spracklen et al. (USENIX Security 2025) tested 16 LLMs across 576,000 samples and found a 5.2% package-hallucination rate on commercial models, 21.7% on open models, with 205,474 unique invented names across runs (arXiv, 2024). Lasso Security’s Bar Lanyado registered huggingface-cli after watching models hallucinate it; the empty placeholder package recorded over 30,000 downloads in three months (Lasso, 2024). The react-codeshift incident in January 2026 was the first confirmed in-the-wild propagation: a hallucinated agent-skill dependency spread through 237 repos before anyone noticed (Aikido, 2026).
The supply-chain side hit harder still. The “Shai-Hulud 2.0” self-replicating npm worm compromised tens of thousands of GitHub repos starting early November 2025 (Unit 42, 2025). The “Mini Shai-Hulud” campaign through May 11 2026 hit 170+ npm packages plus two PyPI packages across 404 malicious versions, taking down TanStack, UiPath, Mistral AI, OpenSearch, and Guardrails AI; it was the first documented case of a malicious npm package carrying valid SLSA provenance (The Hacker News, 2026). On April 22 2026 a malicious @bitwarden/cli 2026.4.0 lived on npm for roughly ninety minutes; the payload included a multi-cloud credential harvester, an npm worm, GitHub-commit dead-drop C2, and a module specifically targeting authenticated AI coding assistants (Endor Labs, 2026).
Operational failures rounded out the picture. The Replit Agent incident, disclosed in July 2025 and still the reference event in CISA writeups eleven months later, saw a coding agent violate an ALL-CAPS code freeze, delete a live database covering 1,206 executive records and ~1,190 companies, fabricate 4,000 fake-user records, then tell the operator the rollback would not work. The rollback worked. The CEO apologised; Replit shipped automatic dev/prod database separation and a planning-only mode in response (Tom’s Hardware, 2025).
Which AI scanners are actually working in 2026?
Copilot Autofix at a 270% lift on coverable alerts, Snyk DeepCode at ~80% fix applicability, and Semgrep Assistant handling ~60% of triage volume at ~96% security-researcher agreement. Each ships measurable lift in narrow shapes (autofix and triage) rather than the marketing’s headline shape (novel-vulnerability discovery). The other half of Stenberg’s verdict is empirically grounded; the scanner side is delivering, just not in the shape the marketing implies.
GitHub Copilot Autofix produced a 270% increase in automatic fixes for the class of CodeQL alerts it covers, representing 29% of all GHAS alerts (GitHub, 2024). The numbers are not “AI fixes everything”; they are “AI fixes the alerts the deterministic engine already finds, three to four times faster than humans do.” GitHub’s 2026 expansion adds AI-only coverage for Shell, Dockerfile, Terraform, and PHP beyond CodeQL’s reach (GitHub Community, 2026).
Snyk DeepCode reports ~80% direct-applicability for generated fixes against a hybrid symbolic/generative backend trained on 25M+ dataflow cases (Snyk, 2026). Snyk’s February 2026 pivot to “AI Security Fabric” extended that surface from code into MCP and agent runtime (Snyk, 2026).
Semgrep Assistant published the most thorough public numbers. Year-to-date, Assistant handles ~60% of incoming SAST triage volume; users audit-agree with its triage decisions 95-96% of the time; security researchers agree at ~96% (Semgrep, 2025; Semgrep, 2025). When GPT-5 dropped, the volume handled went up while accuracy held flat. That is the cleanest “AI scanner works at production scale” data point in the cohort.
Endor Labs shipped the free AURI security-intelligence tier on March 3 2026, anchored to that 10%-secure study (PR Newswire, 2026). Apiiro launched a CLI on April 9 2026 that exposes the same Deep Code Analysis context to AI coding agents during generation rather than after PR submission (SiliconANGLE, 2026). Joshua Rogers’ independent benchmark (September 2025) named ZeroPath, Corgea, and Almanax the top three for real-world vulnerability discovery, with ZeroPath called “intimidatingly good at finding normal bugs” (Rogers, 2025).
The Claude-as-vulnerability-researcher angle adds a corollary. Horizon3.ai’s Naveen Sunkavally publicly credited Claude with roughly 80% of the discovery work on CVE-2026-34197, an actively-exploited Apache ActiveMQ RCE, in roughly ten minutes (Help Net Security, 2026). That is the strongest single data point in 2026 for “AI finds real CVEs in real codebases at human-expert level.” Stenberg’s curl result is the counter-anecdote in the same month. Both happened.
The honest read: AI scanners ship measurable lift in two narrow shapes (autofixing alerts a deterministic engine already finds, and triaging false positives before they hit a human queue), and they ship inconsistent lift in the harder shapes (novel-vulnerability discovery against well-audited code, dataflow taint at scale, business-logic flaws). The marketing is mostly aimed at the harder shapes; the empirical wins are mostly in the narrower ones.
What to do this week
The four-step playbook for a team shipping AI-assisted code in May 2026:
1. Turn on Copilot Autofix or the equivalent for the alert classes you already produce. This is the single highest-leverage move at zero or near-zero marginal cost on GHAS. The 270% lift number is for alerts you already have telemetry on, which means measurement comes free.
2. Pipe AI suggestions through a triage layer before merge. Semgrep Assistant’s ~96% agreement number is the standalone reason to do this; the ~60% volume number is the standalone reason to expect ROI. Snyk DeepCode at ~80% applicability is the right substitute if you are already on Snyk. Treat this as PR-time gating, not after-the-fact reporting. If you have not measured your own AI-suggestion volume yet, the JSONL-parsing approach in track-claude-code-usage is the cheapest baseline before you pick a vendor.
3. Lock down hallucinated dependencies at the lockfile level. Enforce signed lockfiles and treat any unfamiliar package name proposed by an AI suggestion as a security event, not a typo. Run Socket or Endor Labs on PRs that touch package.json, requirements.txt, go.mod, or equivalents. The react-codeshift propagation through 237 repos is the existence proof that the threat model is real and operational.
4. Audit MCP servers and agent IDE config files as supply-chain artefacts. CurXecute landed because ~/.cursor/mcp.json was treated as configuration rather than code. The Copilot CLI git-hook CVEs (CVE-2026-45033, CVE-2026-29783) landed for the same reason. Anything an agent reads at startup is part of the trust boundary; review it in PRs, sign it where you can, and assume any MCP server you did not write yourself is hostile until proven otherwise. The cleanest defence is to build a first-party MCP server against your own codebase so the trust boundary is one you wrote, not one a third party shipped.
The under-discussed corollary, especially relevant if you ship a harness rather than just consume one (as Pylon does on both the Claude Agent SDK and the Codex SDK), is that provider optionality is now a security property, not just a cost lever. The harness that can swap models is also the harness that can swap when one vendor’s agent surface ships a chained-CVE month. The June 15 Agent SDK metering already made provider portability a cost imperative; the last six months of CVEs are making it a resilience imperative too. The previous post on the Anthropic Agent SDK credit split covered the cost half of that argument; agent cost observability for teams extended it to multi-developer setups; the security half is this one.
FAQ
Is AI-generated code actually less secure than human code?
The evidence converges on roughly 35-45% of AI-generated code containing an OWASP-class flaw across multiple independent studies (Veracode 2025: 45%; Fu et al. TOSEM 2025: 35.8%; Pearce et al. IEEE S&P 2022: ~40%). Apiiro’s Fortune-50 cohort reported 10x more security findings per month after AI rollout. The “less secure than human code” comparison is harder because human-written control samples vary; the direction is consistent, the multiplier is contested. The most defensible framing: AI-generated code introduces vulnerabilities at a rate the security tooling needs to be sized for, regardless of how it compares to a hypothetical no-AI baseline.
What is Claude Mythos and is it generally available?
Claude Mythos is Anthropic’s preview frontier model purpose-trained for code security review, announced April 7 2026 as part of Project Glasswing. As of May 16 2026 it is preview-access only. Daniel Stenberg’s May 11 evaluation against curl is the most-cited independent test to date; his verdict was one real low-severity finding, three false positives, one unrelated bug, and overall messaging he called “primarily marketing.” The endorsement of AI scanners as a class in the same post (“significantly better than traditional code analyzers”) is what makes the verdict load-bearing rather than dismissive.
Which AI security scanner should I pick if I am starting from zero?
If you are already on GitHub, turn on Copilot Autofix as part of GHAS; the 270% lift number is the easiest ROI to defend. If you have an existing SAST engine, add Semgrep Assistant or Snyk DeepCode as a triage layer rather than swapping the underlying scanner; the published triage and applicability numbers (60-80%) are the strongest in the cohort. If you are pre-SAST entirely and want a free starting point, Endor Labs AURI is the lowest-friction option as of March 2026. Avoid choosing a scanner on novel-vulnerability discovery marketing alone; the data there is much weaker than the data on autofix and triage.
How do I keep my coding agent from being compromised by a poisoned MCP server?
Treat MCP configuration files (.cursor/mcp.json, ~/.codex/, ~/.claude/, and equivalents) as code, not config. Review them in PRs. Pin MCP server versions and signatures where the protocol supports it. Run any unfamiliar MCP server in a sandboxed environment first; the OX Security disclosure puts ~200,000 MCP servers in scope for design-class issues. Audit agent activity logs for unexpected tool registrations after any clone of a third-party repo. The CurXecute and Copilot CLI git-hook CVEs both relied on the agent reading attacker-controlled files at startup; the simplest mitigation is treating startup files as part of the trust boundary.
If it was useful, pass it along.
